With billions of dollars on the line, it is no surprise that the decentralized finance (DeFi) space has been rife with hacks and exploits on innocent contracts.To name one of the many recent exploits of DeFi contracts, Harvest Finance was hacked for $25-33 million in stablecoins due to a so-called “flash loan attack.” There was an economic logic flaw that Harvest’s developers did not account for, allowing a technically-capable attacker to drain funds.Similar attack vectors have been exploited with contracts like that of Eminence Finance, an Ethereum-based game that users put millions into despite no official launch announcement.
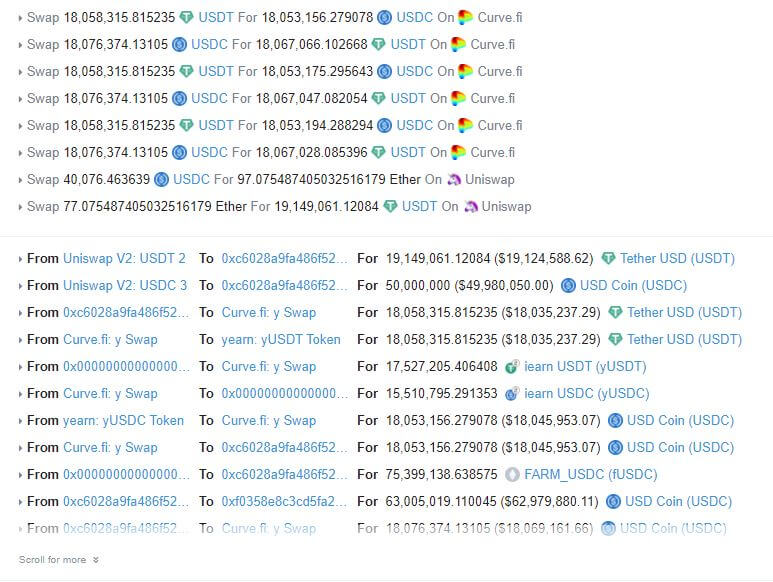
 The hack transactions on EtherscanNot to mention, there are a number of game-breaking bugs that are fixed before they can be exploited. For instance, developers of Yearn.finance (YFI) had to patch a bug that would have allowed a user to steal $650,000 worth of stablecoins from one of its products. The bug was similar to the one used to drain Harvest’s funds.Unfortunately, not all bugs can be caught before they are exploited.Today, around $2 million worth of MakerDAO’s DAI stablecoin was drained from Akropolis. Akropolis is a full-stack DeFi protocol that has a focus on allowing “normies” to save and earn on their stablecoins. Their savings product is the one that was exploited by an unknown attacker.Ethereum DeFi application Akropolis hacked for $2 millionEarly on Thursday, Ethereum analysts and users of Akropolis began to notice suspicious transactions involving Akropolis’ savings product, called Delphi.Quickly, it became clear that an attack had taken place.On-chain data indicated that DAI from Akropolis had been funneled into one address that was interacting with the protocol dozens of times per minute, suggesting something was afoot.Over the span of twenty minutes, the attacker sent dozens of transactions to a number of Akropolis’ Delphi savings pools, draining a sum of DAI from the pool total each time.In all, 2,030,000 DAI had been withdrawn from Akropolis seemingly illicitly.Those stablecoins were sent to an address and have remained there ever since. The seeming attacker has yet to send a transaction from the address where the exploited funds lie.What happened?Crypto-asset auditing and security company PeckShield, which has taken a focus on DeFi over recent months, broke down the details of the attack hours after it happened.To keep it simple, the attacker used a flash loan from dYdX to trick the Akropolis smart contracts into thinking it deposited funds the attacker did not actually have. While some funds were deposited, the attacker was provided liquidity tokens worth more than the amount deposited, creating a discrepancy that could result in large withdrawals from the pool.
The hack transactions on EtherscanNot to mention, there are a number of game-breaking bugs that are fixed before they can be exploited. For instance, developers of Yearn.finance (YFI) had to patch a bug that would have allowed a user to steal $650,000 worth of stablecoins from one of its products. The bug was similar to the one used to drain Harvest’s funds.Unfortunately, not all bugs can be caught before they are exploited.Today, around $2 million worth of MakerDAO’s DAI stablecoin was drained from Akropolis. Akropolis is a full-stack DeFi protocol that has a focus on allowing “normies” to save and earn on their stablecoins. Their savings product is the one that was exploited by an unknown attacker.Ethereum DeFi application Akropolis hacked for $2 millionEarly on Thursday, Ethereum analysts and users of Akropolis began to notice suspicious transactions involving Akropolis’ savings product, called Delphi.Quickly, it became clear that an attack had taken place.On-chain data indicated that DAI from Akropolis had been funneled into one address that was interacting with the protocol dozens of times per minute, suggesting something was afoot.Over the span of twenty minutes, the attacker sent dozens of transactions to a number of Akropolis’ Delphi savings pools, draining a sum of DAI from the pool total each time.In all, 2,030,000 DAI had been withdrawn from Akropolis seemingly illicitly.Those stablecoins were sent to an address and have remained there ever since. The seeming attacker has yet to send a transaction from the address where the exploited funds lie.What happened?Crypto-asset auditing and security company PeckShield, which has taken a focus on DeFi over recent months, broke down the details of the attack hours after it happened.To keep it simple, the attacker used a flash loan from dYdX to trick the Akropolis smart contracts into thinking it deposited funds the attacker did not actually have. While some funds were deposited, the attacker was provided liquidity tokens worth more than the amount deposited, creating a discrepancy that could result in large withdrawals from the pool.
“The exploitation lead to a large number of pooltokens minted without being backed by valuable assets. The redemption of these minted pooltokens is then exercised to drain about 2.0mn DAI from the affected YCurve and sUSD pools,” Peckshield wrote.
Akropolis also responded to the attack, writing that they are reviewing the code and are looking for ways to reimburse users of the protocol that were affected.Only two of the platform’s ten pools were affected by this.